OpenClaw vs Tencent Cloud ADP: Enterprise AI Agent
In-depth comparison of OpenClaw vs Tencent Cloud ADP across security architecture, compliance certification, and data governance.
Summary
Recently, the release of OpenClaw, an open-source personal AI assistant, and its subsequent two rebranding events have attracted widespread attention in the tech community. Its "Local-First" design philosophy and fully open-source characteristics have drawn many tech enthusiasts. Meanwhile, security and compliance have become core considerations for enterprises when selecting AI Agent platforms. This article provides an in-depth comparative analysis of OpenClaw (open-source personal AI assistant) and Tencent Cloud ADP (enterprise-grade intelligent agent development platform) across key dimensions including security architecture, compliance certification, data governance, and permission management, offering objective and professional platform selection decision support for enterprises.
Fundamental Differences in Platform Positioning
OpenClaw: Unique Value of Open-Source Personal AI Assistant
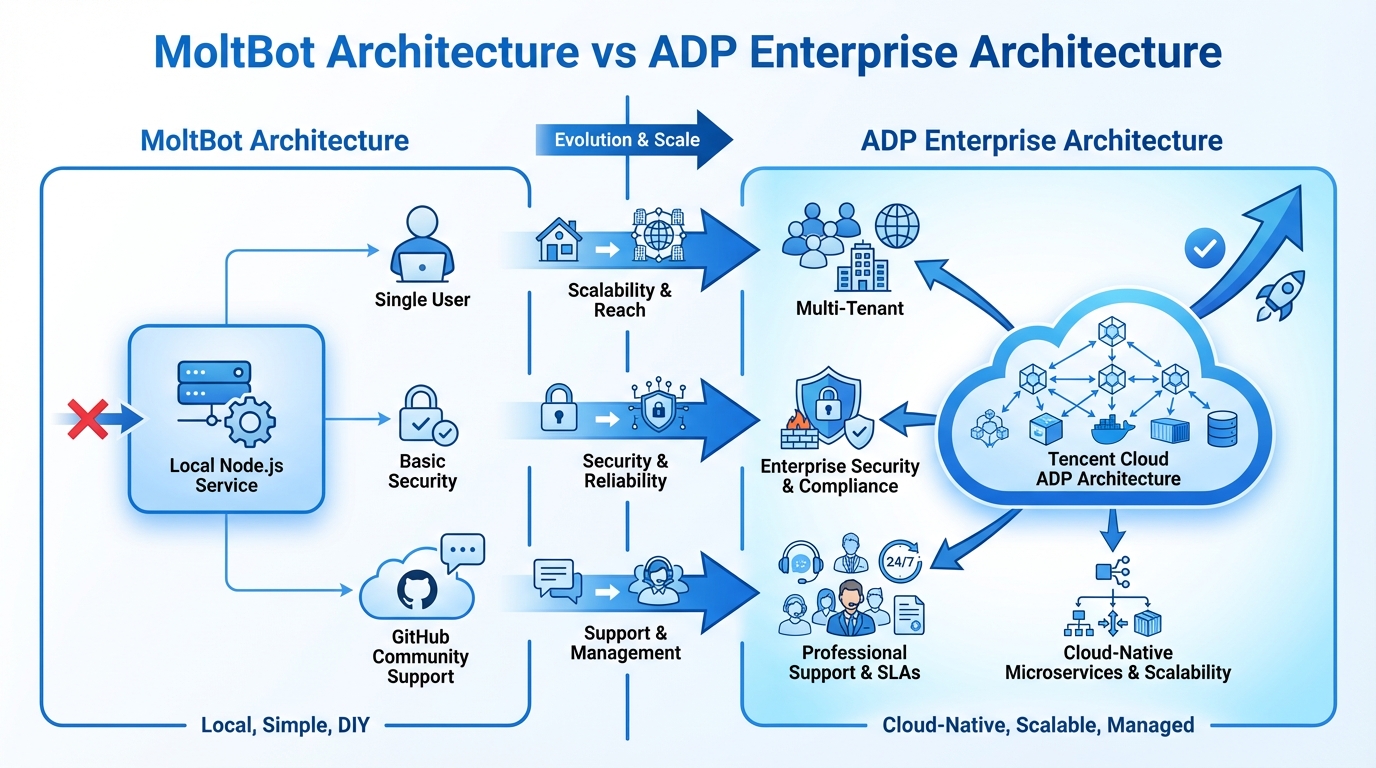
OpenClaw (formerly Moltbot, Clawdbot) is an open-source personal AI assistant project with core design philosophy centered around "Local-First" and "data sovereignty." The project connects local file systems, terminals, and mainstream communication tools through a resident gateway, achieving 24/7 proactive task processing capabilities.
Core Advantages:
- ✅ Data Sovereignty: All data remains on user's local system, users have complete control
- ✅ Open Source Transparency: Fully open-source code allows users to freely audit and customize
- ✅ Deployment Flexibility: Supports local deployment without dependency on external cloud services
- ✅ High Freedom: Users can freely modify code and configure functions according to needs, without platform restrictions
- ✅ Cost Advantage: Open source and free, extremely low hardware requirements (512MB RAM sufficient)
Target User Groups:
- Individual developers and tech enthusiasts with technical backgrounds
- Personal users who want complete control over data storage location
- SOHO office workers needing personal-level automation
- Small teams with limited budgets but technical capabilities
Enterprise Application Limitations:
- Designed for single-user use, lacks multi-tenant architecture
- No support for team collaboration, permission hierarchies, approval processes
- Relies on GitHub community support, no commercial SLA guarantees
- Lacks standardized integration interfaces with enterprise IT systems
Tencent Cloud ADP: Core Advantages of Enterprise Platform
Tencent Cloud ADP (Agent Development Platform) positions itself as a one-stop intelligent agent development framework for enterprises, integrating LLM+RAG, Workflow, and Multi-Agent modes, focusing on solving enterprise pain points in complex business process automation, knowledge base precise Q&A, and stability under large-scale concurrency.
Enterprise-Grade Architecture Design:
- ✅ Cloud-native microservice architecture with elastic scaling support
- ✅ Multi-model unified access gateway avoiding vendor lock-in
- ✅ Low-code orchestration capabilities lowering development barriers
- ✅ Human-in-the-Loop mechanism ensuring business safety
Enterprise Platform Challenges:
- Certain learning curve, requiring teams to adapt to enterprise-grade functions
- Dependency on cloud services, may be limited in unstable network environments
- Relatively higher costs, small teams may face budget pressure
- Rich features but may risk over-engineering
Security Architecture: Different Design Philosophies and Trade-offs
Security Model Risks of OpenClaw
OpenClaw adopts a "user responsibility" security model. While open source facilitates community auditing, it presents significant security risks:
| Security Risk | Specific Manifestation |
|---|---|
| Insufficient Code Auditing | Lacks systematic auditing by professional security teams, potential vulnerabilities may persist long-term |
| Delayed Vulnerability Fixes | Depends on community contributor response, cannot guarantee timely fixes |
| Exposed Attack Paths | Attackers can discover potential attack paths by studying source code |
| Missing Identity Authentication | Lacks mandatory authentication mechanisms, API key leakage incidents have occurred |
Real Case: Many users exposed OpenClaw services to the public internet, leading to frequent API key leakage security incidents due to lack of mandatory identity authentication.
Tencent Cloud ADP Zero Trust Architecture and Multi-Layer Protection
Tencent Cloud ADP adopts a "Zero Trust" security model with the core principle of "never trust, always verify":
| Security Layer | Protection Measures |
|---|---|
| Identity Authentication | Multi-factor authentication (MFA) supporting SMS, email, hardware tokens |
| Tenant Isolation | Independent container namespaces + access control rules + independent storage volumes |
| Data Encryption | End-to-end transmission encryption (national cryptographic algorithms/advanced encryption standards) + static data encryption |
| Audit Monitoring | Full-chain immutable log auditing + 7x24 professional security team monitoring |
Security Certification System:
- ✅ International information security management system certification
- ✅ Third-party operational control audit certification (covering security, availability, and three other domains)
- ✅ National cybersecurity level protection certification, meeting relevant regulatory requirements
Enterprise-Grade Security Trade-offs:
- Strict security policies may affect development flexibility
- Multi-layer security verification may increase user operation complexity
- Dependency on cloud service provider security policies, creating certain vendor dependency
- Security compliance requirements may lead to relatively slower feature iteration speed
Compliance Certification: Open Source Project vs Enterprise-Grade Certification
OpenClaw Open Source Project Compliance Characteristics
As an open-source personal project, OpenClaw has its unique positioning in compliance:
Open Source Project Advantages:
- ✅ High Transparency: Fully open-source code allows users to audit security independently
- ✅ No Vendor Lock-in: Not dependent on specific vendor compliance strategies
- ✅ Flexible Customization: Users can modify code according to their needs to meet specific compliance requirements
- ✅ Community Oversight: Open source community provides additional security supervision
Enterprise Application Compliance Challenges:
- Has not undergone formal third-party security compliance certification
- Most enterprise procurement requires suppliers to provide compliance certification proof
- May face compliance risks when processing sensitive data
- Logs stored as Markdown files lack audit evidence integrity assurance
Tencent Cloud ADP Complete Compliance Certification System
Tencent Cloud ADP has overwhelming advantages in compliance:
| Certification Type | Specific Certification | Enterprise Value |
|---|---|---|
| International Standards | International information security management certification | Covers information security management full lifecycle |
| Operational Audit | Third-party operational control audit | Evaluates design and operational effectiveness of control measures |
| Domestic Compliance | National cybersecurity level protection | Meets important information system compliance requirements |
| Judicial Evidence | Short response time | Provides complete operation logs and audit records |
Regulatory Compliance Capabilities:
- ✅ Full compliance with national cybersecurity, data security, and personal information protection regulations
- ✅ Supports special compliance requirements for finance, healthcare, government sectors
- ✅ Immutable log system ensures audit evidence integrity
Enterprise-Grade Compliance Considerations:
- Strict compliance requirements may limit rapid deployment of certain innovative features
- Compliance certification maintenance requires continuous investment, with relatively high costs
- Different regional and industry compliance requirements may need additional adaptation
- Excessive compliance processes may affect user experience and development efficiency
Data Governance: Local Storage vs Enterprise Framework
Advantages and Limitations of OpenClaw's Local Data Management
OpenClaw stores all data as plain text Markdown files locally, embodying the "data sovereignty belongs to users" philosophy:
Advantages:
- ✅ Users have absolute control over data
- ✅ Data doesn't go through cloud, avoiding cloud privacy leakage
- ✅ Can access historical data even when offline
Limitations:
- ❌ Users need to set backup strategies themselves, easy to forget or misconfigure
- ❌ Local hard drive damage may lead to total data loss
- ❌ Lacks cross-regional disaster recovery capabilities
- ❌ No data lifecycle management functions
Tencent Cloud ADP Enterprise Data Governance Framework
Tencent Cloud ADP establishes a governance framework covering the entire data lifecycle:
| Governance Stage | Core Capabilities | Technical Implementation |
|---|---|---|
| Data Collection | Multi-format support + quality detection | OCR, semantic segmentation, integrity verification |
| Data Storage | Classification + encrypted storage | Graded by sensitivity, KMS key management |
| Data Processing | Auto-desensitization + access control | NLP desensitization technology, RBAC permission management |
| Data Backup | Cross-regional disaster recovery | RPO < 15 minutes, RTO < 5 minutes |
| Data Destruction | Secure destruction + certification | DoD standard auto-destruction, destruction certification |
Data Security Assurance:
- ✅ Multi-replica storage ensures data reliability
- ✅ Automated desensitization of sensitive data (phone numbers, ID numbers, etc.)
- ✅ Fine-grained access control based on RBAC
- ✅ Complete data access and usage behavior records
Enterprise-Grade Data Governance Trade-offs:
- Complex data governance processes may increase data processing time
- Automatic desensitization features may affect data completeness in certain scenarios
- Strict access control may reduce team collaboration efficiency
- Cross-border data transmission subject to stricter restrictions and regulations
Permission Management: Configuration Files vs Enterprise RBAC
Limitations of OpenClaw's Basic Permission Control
OpenClaw defines tool usage permissions through configuration files, using whitelist and blacklist mechanisms:
Permission Control Limitations:
- ❌ Only supports coarse-grained control at tool level
- ❌ No support for defining different user roles and permission levels
- ❌ Lacks multi-level approval and authorization processes
- ❌ Cannot set permission validity periods and time windows
- ❌ Once pairing code is leaked, attackers can bypass audit mechanisms
Tencent Cloud ADP Enterprise Permission Management System
Tencent Cloud ADP implements Role-Based Access Control (RBAC) with fine-grained permission management:
| Permission Dimension | Control Granularity | Implementation Method |
|---|---|---|
| Role Management | Predefined + custom roles | System admin, project manager, developer, etc. |
| Permission Granularity | Resource/operation/field/API level | Controls specific operations on specific resources |
| Identity Authentication | Enterprise integration | Standard authentication protocols, enterprise directory services, MFA |
| Approval Process | Multi-level approval authorization | Supports complex enterprise approval processes |
Enterprise Identity Authentication Integration:
- ✅ Single Sign-On (SSO) supporting standard authentication protocols
- ✅ Integration with enterprise directory services or Active Directory
- ✅ Automatic synchronization of organizational structure and user information
- ✅ Multi-factor authentication supporting various authentication methods
Enterprise-Grade Permission Management Challenges:
- Complex permission systems require professional administrators for configuration and maintenance
- Overly granular permission control may lead to increased management complexity
- Enterprise system integration may require additional technical investment and debugging time
- Permission changes and approval processes may affect business response speed
Operations Monitoring: Community-Driven vs Enterprise SLA
Risks of OpenClaw's Community-Driven Operations Model
Although OpenClaw has extremely low hardware requirements (512MB RAM), operations support presents major risks:
Operations Risk Assessment:
- ❌ No Service Level Agreement (SLA) guarantees
- ❌ System availability completely depends on user self-maintenance
- ❌ Problem resolution depends on community response speed and willingness
- ❌ Vulnerability fix cycles may range from days to months
Tencent Cloud ADP Enterprise Operations Monitoring System
Tencent Cloud ADP provides clear enterprise-grade SLA guarantees:
| SLA Metric | Commitment Standard | Assurance Measures |
|---|---|---|
| Recovery Time Objective (RTO) | ≤ 5 minutes | Automatic failover + professional operations team |
| Service Availability | ≥ 99.95% | Multi-node deployment + real-time monitoring |
| Monitoring Metrics | 20+ core metrics | Full coverage of performance, business, security metrics |
| Technical Support Response | 15 minutes - 16 hours | Tiered support services |
Intelligent Alert System:
- ✅ Supports multiple alert methods: enterprise WeChat, SMS, email, phone
- ✅ Categorized by severity: urgent, important, general
- ✅ 7x24 professional operations team continuous monitoring
- ✅ Service fee compensation when SLA commitments are not met
Enterprise-Grade Operations Trade-offs:
- Professional operations services require corresponding cost investment
- Strict SLA requirements may limit deployment of certain experimental features
- Multi-layer monitoring and alerts may create information overload
- Dependency on cloud service provider operations capabilities, creating certain technical dependency
Content Security: Flexibility vs Compliance Assurance
Risks of OpenClaw's No Default Security Guardrails
OpenClaw pursues high-privilege execution capabilities with no default "security guardrails," bringing serious security risks:
Content Security Risks:
- ❌ No content review for user input and AI output
- ❌ May leak sensitive information like passwords, keys, personal privacy
- ❌ Highly susceptible to Prompt Injection attacks
- ❌ May lead to local sensitive files being packaged and leaked
Real Attack Scenarios:
- Direct injection: Attackers bypass system restrictions through carefully crafted prompts
- Indirect injection: Inject malicious instructions through external data sources like web pages, files
- Jailbreak attacks: Break through AI security restrictions through specific prompt patterns
Tencent Cloud ADP Multi-Layer Content Security Protection
Tencent Cloud ADP has built-in powerful content risk control modules providing multi-layer security protection:
| Protection Layer | Protection Measures | Technical Implementation |
|---|---|---|
| Input Review | Sensitive word filtering + intent recognition | Based on sensitive word database + NLP technology |
| Output Review | Real-time content review + risk scoring | Detects illegal, violent, pornographic risks |
| Data Desensitization | Auto-desensitization of sensitive info | Identifies names, phone numbers, ID numbers, etc. |
| Rule Engine | Custom review rules | Supports industry templates + rule version management |
Industry Compliance Support:
- ✅ Provides review rule templates for finance, healthcare, education industries
- ✅ Automatic interception of violating content with one-click rollback support
- ✅ Provides compliant alternative output content
- ✅ Sensitive word database dynamically updated based on latest regulations and policies
Enterprise-Grade Content Security Trade-offs:
- Strict content review may misjudge normal content, affecting user experience
- Multi-layer protection mechanisms may increase system response time
- Industry-specific rules may limit cross-industry application flexibility
- Excessive security protection may suppress innovation and personalized expression
Technical Support: Community Collaboration vs Professional Services
Uncertainty of OpenClaw Community Support
OpenClaw technical support completely relies on the open-source community:
Support Model Risks:
- ❌ Problem response time ranges from hours to weeks
- ❌ Problem resolution depends on community member technical levels
- ❌ No clear responsible party when problems occur
- ❌ No compensation for service interruptions or data loss
Tencent Cloud ADP Professional Technical Support System
Tencent Cloud ADP has professional technical support teams providing multi-tier graded services:
| Support Level | Response Time | Service Content |
|---|---|---|
| Basic | 16 hours | Ticket support + documentation support |
| Developer | 8 hours | Ticket + phone + remote assistance |
| Business | 30 minutes | Dedicated support + regular reviews + architecture consulting |
| Enterprise | 15 minutes | 7x24 dedicated + on-site support + custom services |
Value-Added Service System:
- ✅ Architecture consulting services (solution design, technology selection, performance optimization)
- ✅ Custom development services (requirement analysis, custom development, integration services)
- ✅ Training services (product training, technical training, certification exams)
- ✅ Dedicated services (dedicated account manager, regular reviews, priority support)
Professional Service Considerations:
- Professional technical support services require corresponding cost investment
- Tiered services may result in different users receiving differentiated support experiences
- Dependency on service provider professional capabilities may create technical dependency risks
- Enterprise-level service complexity may increase communication and coordination costs
Enterprise Selection Decision Recommendations
Applicable Scenario Analysis
Based on in-depth comparison across eight dimensions, the applicable scenarios for both platforms differ significantly:
OpenClaw Applicable Scenarios:
- ✅ Experimental projects for individual developers and tech enthusiasts
- ✅ Personal users or small technical teams with security technical capabilities and desire for complete data control
- ✅ Budget-limited scenarios that can accept no SLA guarantees
- ✅ Personal use scenarios without enterprise compliance requirements
Tencent Cloud ADP Applicable Scenarios:
- ✅ Production environment applications for medium to large enterprises
- ✅ Finance, healthcare, government sectors with strict security compliance requirements
- ✅ Scenarios requiring stable and reliable technical support and SLA guarantees
- ✅ Scenarios requiring integration with existing enterprise IT systems
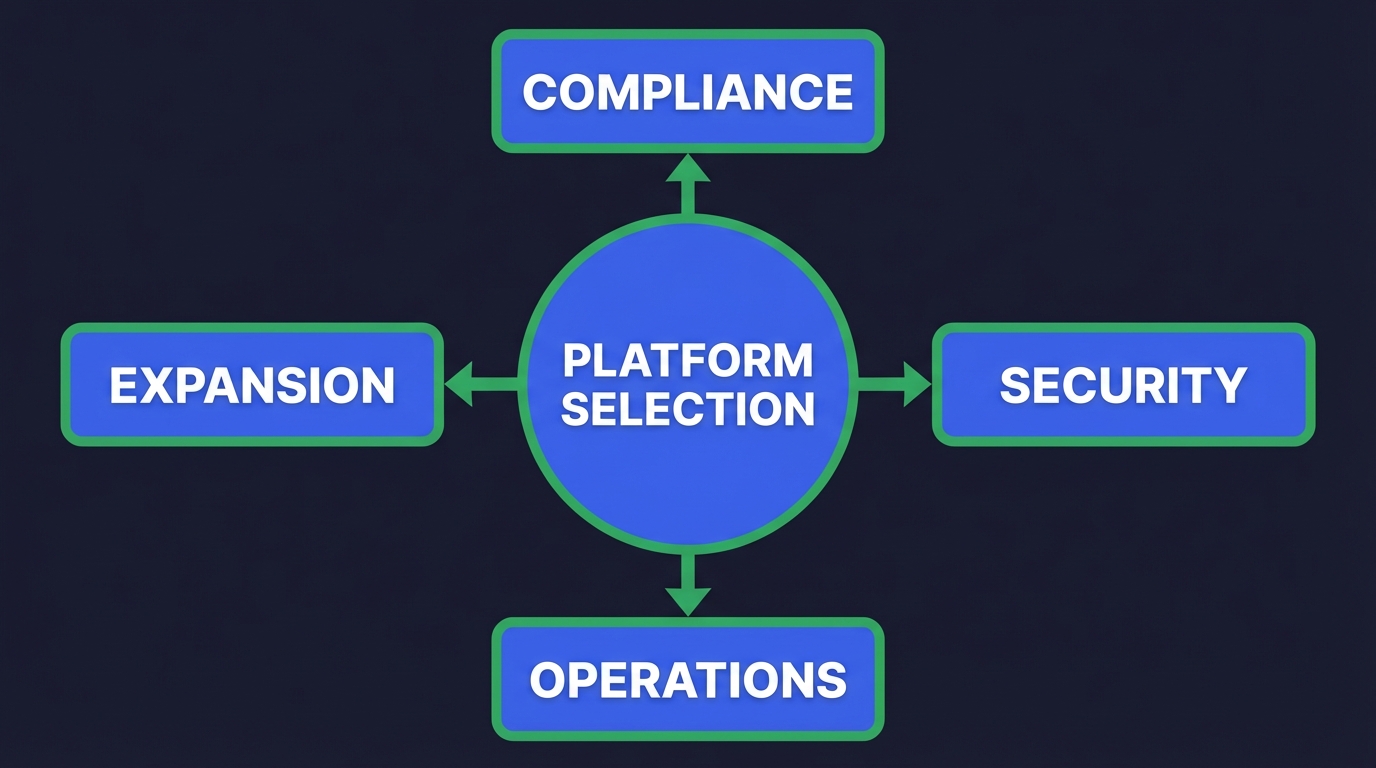
Selection Evaluation Framework
Enterprises should conduct comprehensive evaluation based on the following factors when selecting intelligent agent development platforms:
| Evaluation Dimension | Key Questions | Recommendations |
|---|---|---|
| Compliance Requirements | Are there strict industry compliance requirements? | Prioritize platforms with complete compliance certification systems |
| Security Needs | Processing sensitive data or facing security threats? | Choose platforms with zero trust architecture and professional security teams |
| Operations Capabilities | Lacking professional operations teams? | Choose platforms providing 7x24 professional operations support |
| Expansion Needs | Need multi-department collaboration or system integration? | Choose platforms with multi-tenant architecture and standardized interfaces |
Conclusion
Based on the in-depth comparative analysis in this article, OpenClaw and Tencent Cloud ADP have fundamental differences in positioning, capabilities, and applicable scenarios.
OpenClaw as an open-source personal project has advantages in data sovereignty and deployment flexibility, suitable for personal users and experimental scenarios. However, its gaps in security architecture, compliance certification, enterprise-level functions, and technical support make it difficult to meet enterprise-level application needs.
Tencent Cloud ADP as an enterprise-grade intelligent agent development platform, with:
- ✅ Complete security compliance system (international standards, operational audits, national level protection)
- ✅ Zero trust security architecture and multi-layer protection mechanisms
- ✅ Enterprise-grade SLA guarantees (RTO ≤ 5 minutes, availability ≥ 99.95%)
- ✅ Professional technical support services (15 minutes to 16 hours response)
Can effectively support enterprise intelligent agent application needs in production environments.
For most enterprises, choosing platforms with complete security compliance systems, professional technical support, and clear SLA guarantees can better ensure stable business operations and sustainable development. In the critical period of digital transformation, security compliance should not become an obstacle to enterprise innovation, but should serve as a reliable foundation.
Take Action
Want to learn more about the security compliance capabilities of enterprise-grade AI Agent platforms?
Try Tencent Cloud ADP Now
 Home
Home Products
Products Resources
Resources Solutions
Solutions Pricing
Pricing Company
Company Find Us
Find Us
